The book of spells
A quarter of a century
It has been almost 25 years since the first time I met Linux – I’m having my first gray hair indeed. I’ve been enchanted by it and I wanted to become a professional.
When I started we could install it from scratch, although the first distros were beginning to pop up … Slackware, Suse, Red Hat – not Red Hat Enterprise Linux, only Red Hat.
Me, as many others, was bold enough to use file systems such as ext2: it was risky not to use a journaled filesystem, but it was what we had, and we were stubborn enough to keep on until ResierFS and ext3 popped up. Printing was a nightmare and the layered design to support hardware devices, especially audio, was a mess (Ok, audio is still a mess, but this does not really matter on servers).
And what about the X-Window system – keep in mind that security has been designed according to the sensitivity of the mid of the ’80, but the overall design was impressive – you launch an application and it is rendered on the connected graphical display, … wherever it is.
Me, as many others, hung on because we were sure that Linux would have become one of the most used operating systems for mission critical workloads.
An operating system fully open, that we can just use, or deeply explore if we wanted to. That was exactly what I wished.
For most of us Linux means freedom, the same way the Black Pearl sounds like freedom to Captain Jack Sparrow.
Sysinit, Upstart and now systemd, … what a long way we had together; we both were young, but now I consider both of us mature: that’s why I think that it has come the right moment to share some of my notes on what I did with Linux during all of these years.
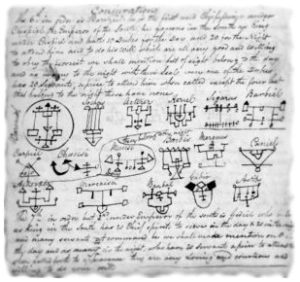
Over the years I started considering them as spells – some of them are really powerful, and I put them into my own grimoire.
Of course I do not consider them the only way of doing things, but they are what let me gradually grow as a modern Linux professional.
Of course there are other grimoires out there with other spells: this is mine, and I hope you’ll love it.
A modern Linux professional
A modern Linux professional should not only be able to operate and troubleshoot Linux: he should also have all of the soft skills required to design and implement mission critical infrastructures applying commonly used frameworks in compliance with regulators.
He should know how to operate under environments subjected to change management, as well as be able to cooperate with other team members to fulfill a project, tracking the progress to ease the governance.
And of course, he should master legacy technologies, as well the most modern ones: a lot of modern technologies relies upon old concepts and tools under the hood: there's a huge difference from operating a technology and be conscious of everything about it, be aware of its limits and know the features that can be exploited to integrate with other technologies.
But most of all, he should be positive and humble so as to contribute to the creation of a nice working environment where everyone should be proud to belong to the team, eager to meet its colleagues to share experiences and ideas.
Is Linux the best operating system in the world and do the others not worth anything? Naaa, mate, flame wars are for newbies, and religions are for priests and sorceress. We are professionals: it's another matter.
These are the topics I want to talk about in these blog pages. I hope you will enjoy them, and why not, connect each other professionally on Linkedin
Search Post
Please use the following search box to see if there is any post you are interested into:
or click here to get access to the full blog.
Recent Posts
This is the list of the more recent spells of the grimoire:
- Kubernetes Backup – perform Gitea backup on S3 with MinIO - When dealing with Kubernetes, backing up an application's data is not as straightforward as when the application is installed directly on your system. Due to its design, Kubernetes orchestrates applications to make them resilient by horizontally scaling them as needed and restarting them upon failure. This often results in applications being started or restarted on […]
- Vagrant Box Catalog And Vagrant Box Repository Tutorial - As we saw in the Vagrant - installing and operating post, Vagrant provides a convenient way for automating the setup, configuration and management of virtual machines, enabling reproducible and consistent development environments. In that post, we also had an overview of how to create a Vagrantbox from scratch for the Parallels provider. We then digged […]
- Create Oracle Linux 10 aarch64 Vagrantbox for UTM - On Apple Macs with Silicon processors, UTM is one of the best free virtualization options available, offering solid performance for ARM-based virtual machines. As we saw in the Vagrant - installing and operationg post, Vagrant provides a convenient way for automating the setup, configuration, and management of virtual machines, enabling reproducible and consistent development environments. […]
- Python Smtplib Tutorial – howto send HTML EMAIL with Python - The Python Smtplib Tutorial - howto send HTML EMAIL with Python is explains how to send HTML emails using SMTP, including auth, SMTP with TLS and SMTPS. After introducing Python smtplib, the post provides an hands-on example showing how to add HTML email notification to an existing scirpt. The provided code supports every kind of […]
- Python Argparse Tutorial – Argparse HowTo - The Python Argparse Tutorial - Argparse HowTo post provides a practical example of how to parse command line parameters and options using the argparse module. Knowing how to add command line paramenters and options to Python scripts is a must-have skill, since it enables them to better adapt to customers' needs, allowing them to enable […]
SKILL SET EVERY PRO SHOULD HAVE
THE PILLARS
There are pillars every Linux professional should have: a good understanding of data formats, of data search and manipulation tools and, although this one is often neglected, of encryption technologies, to guarantee data integrity and confidentiality both on the disk and the wire.
SYSTEM ADMINISTRATION
Professionally administering Linux based systems requires a lot of experience: Linux itself provides only the POSIX compliant kernel, but there are a lot of other applications and tools that should be thoroughly known, and even the most legacy ones may still be suitable to some use cases.
SCRIPTING
One of the things that makes UNIX-Like - and so Linux - so attractive is certainly the powerful scripting that can be done with it: automating repetitive tasks, automating housekeeping and such are only the most trivial things that can be addressed by using scripts.
VIRTUALISED INFRASTRUCTURES
Linux is a very good platform even when it comes to virtualising systems - there are several full-featured products - Red Hat's RHEVM and Oracle's VM are probably the most used, but you can virtualise things also using very basic tools such as KVM and libvirt.
HIGH-AVAILABILITY
It is impressive the high-availability that the Linux platform can provide: high available applications, clustered file systems over redundant storages. Designing and implementing clusters is a fine art that requires a lot of experience and skills, but the outcome can seriously impress people.
SYSTEM INTEGRATION
Applications are designed to use a lot of protocols and standards: it is quite rare to find skilled professionals that thoroughly know them, but these professionals are the ones that can make the glue between development teams and system engineering teams, ... besides quickly troubleshoot unexpected integration issues.
DEV-OPS TOOLS
Dev-Ops philosophy has brought into the System Operations field tools that were previously used by developers only. It is very challenging,since besides these tools, professionals should also have a good understanding of modern frameworks and methodologies such as SCRUM and Lean.
DESIGNING
Being able to design requires a lot of skills: it is not enough to just know what is the right software that meets the requirements. Everything should be carefully checked by the security perspective, and particular care should be taken for the usability: the weak ring of everything are the users, since they are human beings.
ABOUT ME


Well, ... a little bit of space to introduce myself: Marco Carcano, pleased to meet you. I cut my teeth working as a developer, but I quickly realized that I preferred working as a system engineer and so I gradually moved to this field. I worked on both Linux and Microsoft environments until 2012, then I decided to specialize on Linux only: anyway the high skill level gained on Microsoft platforms too during the years let me still easily design and implement cross-environment solutions.
I have a preference for Red Hat: this is the list of Red Hat certifications I succeeded into indeed
- Red Hat Certified Specialist in Advanced Automation: Ansible Best Practices
- Red Hat Certified Specialist in Ansible Automation
- Red Hat Certified Specialist in Configuration Management
- Red Hat Certified Specialist in OpenShift Administration
- Red Hat Certified Specialist in Gluster Storage Administration
- Red Hat Certified Specialist in High Availability Clustering
- Red Hat Certified Specialist in Server Security and Hardening
- Red Hat Certified Specialist in Deployment and Systems Management
- Red Hat Certified Specialist in Virtualization
- Red Hat Certified Engineer
- Red Hat Certified System Administrator
Besides Red Hat Certified Engineer, the specialization exams entitled me as:
- Red Hat Certified Virtualization Administrator,
- Red Hat Data-center Specialist
- Red Hat Certified Architect (Data-center concentration)
Besides this I also have been Cisco CCNA, and I'm ITILv3 certified too. Currently I'm working in the financial field as a senior professional, both providing support to less “seasoned” colleagues as well as designing and implementing mission critical solutions, often with the bleeding edge technologies.







